Anyone who maybe considering their career choices will have noticed that there are a lot of job openings in the cybersecurity space. Every week someone, somewhere, is trying to hire a cybersecurity professional, or so it seems. The job ads are full of openings and anyone with 'cybersecurity' on their Linkedin profile or online resume is probably getting connection requests from recruiters like they just won a large sum of money and offered to give it all away.
According to the Cisco Annual Cybersecurity Report for the past 5 years in a row, there has been a consistent 12x demand over supply for qualified, certified or experienced, security professionals. That means that there's currently 12 open security jobs for every person able to fill that role. With statistics like that, cybersecurity professionals will never be out of a job for long.
Over the past couple of years, demand for cybersecurity staff has literally gone through the roof as one attack follows after another and private and public sector organizations have woken up to the fact that they need more help. In fact, by 2025, it is estimated that there will be 3.5 million unfilled cybersecurity jobs in the USA alone.
The cyber worker shortage is a particular problem with smaller organizations, everything from municipalities and law firms to hospitals and businesses, that can’t offer high enough pay to attract high-skilled workers, according to the SANS Institute. In 2020, the annual mean wage for information security analysts was $107,580, almost double the mean for all U.S. occupations combined, according to data from the Bureau of Labor Statistics. But it's not enough to meet demand and organizations are having to get creative to attract cybersecurity staff.
The real problem however, is that the United States and many other OECD countries aren't training enough people in high school, university or in technical / vocational colleges.
'Vocational' versus 'Professional'
With statistics like these it's a wonder that more people aren't running towards a career in cybersecurity, but there are barriers to entry. A clean criminal record is usually required unless you can explain yourself out of prior wrongdoings. Security staff usually have access to all kinds of elevated access permissions in order to do their jobs and no one wants a potential insider working against the team. The classic Catch-22 experience trap that I'll address in more detail later, and finally the professional versus vocational dilemma, all of which confuse successful entry.
A college degree is usually not needed for a vocational job, but it is often required for professional jobs. And in the cybersecurity space the prevailing thought is that security practitioners are professionals, thus the majority of advertised positions require a degree. A recent (ISC2) report indicates that 86% of the current cybersecurity workforce has a bachelor's degree or higher. Furthermore, a quick search on Indeed.com shows about 46,000 cybersecurity jobs, of which 33,000 (>70%) require a degree.
However, ask anyone working in the cybersecurity field whether a degree is really needed for many cybersecurity positions and they would probably tell you no. What is more important they will tell you is aptitude, ability and willingness to learn, and some security experience. By posting job postings that require a degree for lower level jobs, HR and hiring managers are actually disqualifying many deserving candidates perfectly able and willing to take on that role. And because these potential candidates don't have a degree, they are usually less expensive to hire.
Everything is negotiable
Don't have a college degree but keen to work in security? Tenacity and persistence usually pays off - especially in a tight labor market. If you can show sufficient enthusiasm, passion, and willingness to learn including self-study you have undertaken then chances are you can still get an opportunity to prove yourself. Security Hiring Managers would much rather have someone on their team who is keen, and ready and willing to learn, than someone who has countless degrees and believes that they don't have to prove anything to anyone and may believe they can just cruise through life. But experience is also a factor and there lies the classic Catch-22.
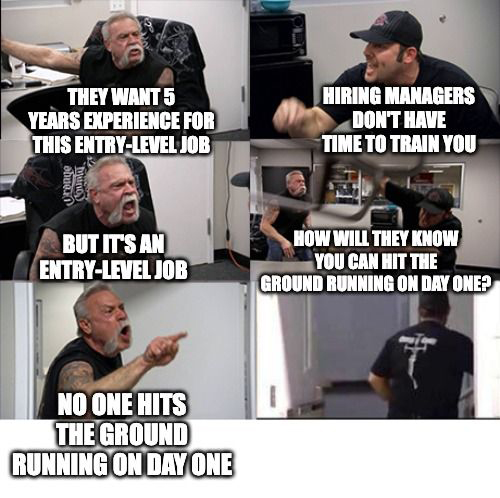
How do you gain the 'experience' that everyone is asking for to get the job in the first place? Well, sometimes it can be a bit of a Catch 22 - and that's a bit of an understatement. Just read some of job postings requiring 'n' years experience for an 'entry' level position plus a current CISA, CISM or CISSP certification, the latter of which seems to have become a common entry requirement.
For those who haven't yet come across the CISSP which stands for Certified Information Systems Security Professional, it's a grueling 6 hour long multiple choice exam where every answer is correct but one is more correct than the others. But in addition to passing the exam, in order to become a CISSP, you also need 5 years of experience, or 4 years experience plus a Masters Degree in cybersecurity or a related field.
Its the classic Catch-22 - you can't get the job without the CISSP and you can't get the CISSP without the job experience!
Its also difficult though not impossible to to pass the CISA or CISM certification without at least some experience.
The truth is that job postings are written by HR professionals, most of whom have very little understanding of what the actual job they are hiring for involves. Someone should make a Hollywood movie about it and call it "Recruiters are from Mars" because they might as well be.
A classic example of this was a job posting I saw last week that wanted someone with ten years experience of Kubernetes. However Kubernetes is only five years old as a technology, so no one could possibly have more than five years experience. This post of course was quickly noticed by the security community and the job posting became the center of ridicule for a few days before it was taken down. Not only did it make a mockery of the reputable company that had posted it, (I won't mention their name, but needless to say they should have known better), but it highlighted the problem of unrealistic job posting requirements.
Someone should make a Hollywood movie and call it "Recruiters are from Mars" because they might as well be.
Whether the problem ultimately lies with HR, recruiters or hiring managers, there is an unreal expectation in the cybersecurity space. This is a highly, highly, competitive space for scarce security resources and company salary scales are often totally out of touch with market rates. As an example cybersecurity professionals currently make at least 25 to 30 percent more than their peers in IT with the same years of experience and equivalent number of qualifications. Despite this, companies often use the same salary matrix for IT and cybersecurity staff given that security still reports into IT in many organization, often at the CIO level. The result is that to attract any candidates HR has to post more senior roles with higher salaries to find candidates willing to consider working for the company in the first place.
Some of the job postings that demand all kinds of experience would probably command a salary package of at least a million dollars a year if someone had all of those skills, certifications and experience. While I would like to believe that security professionals in their 30s and 40s are making seven figure salary packages, that probably isn't the case for most. In other words, JOB REQUIREMENTS are nothing more than a WISH LIST.
Treat the 'JOB REQUIREMENTS' as 'DESIRED SKILLS'
But it's not just experience, the same is true for security certifications and academic qualifications.
Any recruiter claiming that 'x' security experience, plus 'y' certifications, plus 'z' masters or doctoral degrees is a MUST HAVE, simply couldn't afford to hire that candidate if he or she walked through the door tomorrow. And don't think that working in cybersecurity is a 'boys club' and not open to other sexes either. There is a steadily and growing chorus of very capable women making their mark at every level of the profession - many as CISO.
In other words, you should apply anyway. It might not work all of the time but you only need it to work once to get your foot in the door. It is after all, getting more competitive each year as more and more companies attempt to hire the few security resources that might be looking. Increasingly, companies are having to re-think who they hire, at what level, and what skills are really necessary. They are taking what they can get and providing on-the-job training instead, in order to fill vacancies and get backsides in seats. If a security job has been posted for a long time it probably means that the company is having difficulty filling the position. That might spell 'opportunity' for some.
Companies looking for security certifications will usually pay for the training, the materials and the examination if they want you to obtain one. While the Catch-22 nature of the CISSP might be out of reach for entry level candidates, get yourself certified in an easier credential such as the CompTIA Security+ or some of the SANS GIAC foundational courses. I am also a fan of the ISACA certifications CISA, CRISC, CISM, etc, and cover much of the material for these certs in the masters courses I teach at University of Denver University College. CompTIA Security+ is also included in many of the Associates Degree programs at your local community college and there are usually educational grants and stipends available to cover your fees. You just need to put in the work and most courses now are available online so you can study at nights and weekend from your home after family dinner or putting kids to bed. So you can kill two birds with one stone if you plan your study well and come out with a degree and some certifications at the same time.
A basic security certification combined with a desire to work towards a higher more widely recognized certification or qualification, and an interest and aptitude in cybersecurity might be enough to get you past a CISSP 'required' in the HR job posting and on to the next level with a Zoom or WebEx interview with the security team.
The same is true with academic certificates and degrees. Most universities are now running courses on-line thanks to COVID and many have solid cybersecurity programs at the Associates, Bachelors and Masters level. That allows you to shop around for the best course from the best university at the best price from any reputable university in the world.
The US has way too many online cybersecurity degree programs to mention here, and the UK and Australia have pivoted most of their 'on-site' programs to 'on-line' as a result of COVID, especially at the masters level. Finally, don't be put off by degree programs in non-English speaking countries, many cybersecurity programs like Germany are taught in English, are incredibly high quality, and are way less expensive than elsewhere.
There are many government grants, and university stipends available for those willing to dig a bit. Companies will also often pay for you to study for degree or certificate.
These education benefits are sometimes capped at $5,000 to $10,000 a year so you may have to plan accordingly and space out your classes to have them fully covered. On a four quarter academic system, pay for Fall and Winter Quarters in one calendar year and expense those fees, then take a course every other Quarter till you are done and have that degree certificate in your hand, all paid for by your employer. This benefits you and may result in a pay raise. It also benefits your employer since you are better skilled and qualified now and they can do more with you - like promote you into a leadership position.
It may take you several years of part time evening or weekend study, but a degree will boost your career opportunities as well as salary expectations so is most definitely worth your time. It may also exempt you from having to keep up with professional certifications like the CISSP, and pay these commercial bodies annual membership fees which can be expensive and annoying.
But How Do I Get Past Automated HR Systems?
Before ubiquitous use of the internet applying for a job involved typing up your resume or CV, making photocopies, and handwriting a cover letter for each job you wanted to apply for and then mail that package into the company. There was a cost in time and materials and this forced people to target the jobs they REALLY wanted to apply to. In the final year of my undergraduate degree, I spent several weeks mailing out over 50 hand written cover letters and resumes to companies I wanted to join on obtaining by bachelors degree. None were successful. Many to this day, never bothered to acknowledge my application or politely decline my application. A broadcast approach to job search didn't work then just as it doesn't work now.
Step forward several decades and today a candidate can blast off thousands of job applications with the click of a button. Linkedin and a heap of other web sites and services will even match your skills and experience to posted job openings and apply automatically for you. Its doubtful many candidates will even remember the names of the companies that they have applied to via these tools, especially if it was weeks ago. The result is, that today employers receive tens of thousands of resumes from all directions for a single job posting.
To cope with this deluge, most companies, somewhat to their detriment, are using automated resume scanning systems to narrow down the thousands of applications they receive. According the Wall Street Journal and a recent Harvard Business School Study these systems are filtering out thousands of good candidates; candidates that would be a good fit for the job if only they could only get in front of the hiring manager.
"Job prospects get tripped up by everything from brief résumé gaps to ballooning job descriptions from employers that lessen the chance they
will measure up. Lead Harvard researcher Joseph Fuller cited examples of hospitals scanning résumés of registered nurses for “computer
programming” when what they need is someone who can enter patient data into a computer."
You might like to review your resume and fill in any employment gaps with volunteer work or study you were involved in between paid jobs. Gaps for pregnancy, child rearing, travel or overseas postings as a military spouse also need to be filled. Neither computer systems or recruiters like to see gaps where you did nothing for 6 months or more. As for missing certifications, you might be able to get past that by adding to your resume that you are currently studying for the CISSP, the CISA or some other "required" certification.
You might also want to try the backdoor if the front door to a company is locked. Farm your contacts on Linkedin for connections you might have to someone who knows someone who might be able to make a call or shoot an email to the right person for you with an introduction. Its all about WHO you know, whether that's directly or not. I get hit up all the time - everyone from distant relatives, to old workmates and colleagues, to former students wanting to see if I can make a warm intro for them somewhere.
Finally, you could research who the hiring manager is, or his or her boss and try and connect with them yourself via Linkedin or some other means without a warm introduction. It shows initiative and persistence. Companies would much rather hire someone who REALLY wants to work for them than simply the best candidate on paper.
If a candidate can be found without cost i.e. direct via an internal recommendation rather than through a recruiter then this could be to your advantage. Head hunters typically charge between 20% and 35% of starting salary in fees to introduce screened candidates which can be expensive. Going direct may help you to negotiate a better base salary and sign-on bonus also, since there are no indirect costs to hire you.
But you as a candidate need to start somewhere.
In the following 90 minute video, I outline:
- What is cybersecurity and why is it front and center as we adopt increasing levels of automation and digitalization?
- Who are the main perpetrators of cyber attacks and what are their motivations?
- Why is cybersecurity so important today?
- What are the security frameworks being used to secure organizations?
- Why you should consider a career in cybersecurity
- What are those opportunities?
- How to develop a cybersecurity career strategy
- What security certifications and qualifications should you consider?
A PDF of this presentation can be downloaded or viewed here:
http://pubs.cyberthoughts.org/A_Career_in_Cybersecurity.pdf
http://pubs.cyberthoughts.org/A_Career_in_Cybersecurity.pdf
Useful References and Further Information
This post was updated 2021.09.05 with links to the Harvard Business School study above and again on 2021.09.21 with links the the CSO article on CRISC.
Original stories and articles may be republished without charge provided that attribution is provided to the source and author. Articles written for, and published first elsewhere, are subject to the republishing terms and conditions of the host site.