“The digital canary in the digital coal mine”
A “canary in the coal mine” is an idiom that refers to an early warning sign for upcoming trouble. This comes from the day when there was no technology to detect leaks from unseen pockets of toxic gas in the rock of a coal mine. Canaries are more sensitive to the toxic gas in the mines than humans so miners used to take poor canaries with them as an early warning sign of toxic gas. If the canary is on the bottom of the cage it’s time to get out of the mine FAST! So how does this relate to ransomware – bear with me for a while and I will explain how ransomware is the early warning sign that security threats have a free rein in your environment.
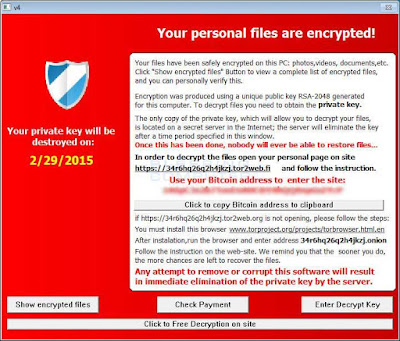
Ransomware is big business today. Ransomware miscreants encrypt a victim’s files and only provide the decryption keys after the victim pays the “ransom”—usually in the vicinity of $US300 to $US500. Unlike most other online crimes that target businesses exclusively, ransomware impacts end users directly. Ransomware campaigns are not discrete about their victims as this is a volume game and the bad guys will attempt to compromise tens of thousands of victims per day whether they be a grandparent at home looking at photos, or a corporate banker making billion dollar deals. The pay day for their efforts can be staggering. Cisco recently worked with Level 3 Threat Research Labs to disrupt an Angler exploit kit botnet which Cisco estimates to have be earning at least $US30M annually and I hope this disruption hurt the bad guys.
The effectiveness of Ransomware can be seen in a recent CERT Australia survey where 72% of companies reported malware incidents in 2015 which has more than quadrupled since 2013 (17%). 72% of respondents also stated that Ransomware “is the threat of most concern”. These figures are staggering when the survey is targeting corporations and it’s not surprising as I have seen ransomware execute and encrypt data on ASX Top 200 companies' systems and Fortune 100 enterprise servers as well as our relatives' laptops. Quite frankly, ransomware is everywhere and one of the key reasons why it’s a huge concern is that signature based anti-malware products such as anti-virus are mostly ineffective as ransomware is written and tested to avoid detection by AV products and the signatures can change hundreds of times in rapid succession.
Now let's get back to the “canary in the coal mine” analogy. I believe that the most troubling aspect of ransomware is NOT its effect on the end user, but more that it is so incredibly effective in:
- Penetrating corporate network perimeter defences
- Able to execute as a new process on a victim machine
- Call out to a server on the Internet to download an encryption key (refer to the update below)
- Typically, the first time anyone detects the malware is because their work files (or cat videos) cannot be accessed because they are encrypted
I often get asked “can you restore my files?” Unfortunately, the answer most often is “No”. Ironically most ransomware uses strong and well implemented cryptography and it is not economically or technically viable for anyone to attempt decryption. The point here is that we need to move on from believing all attacks can be prevented; we also must realise that attacks must be detected quickly to prevent damage to the business. The fact that most attacks are not directly detected by the victim, but by the action of the external party (encrypting data) is what really troubles me as a security professional. Security controls should be preventing as close to 100% of attacks as possible, but there remains a fraction of successful attacks that we must detect and respond to before significant damage is done to our businesses.
I think we should be closely looking at the lessons we learn from ransomware to show us how effective our security preventative and detective controls are, and how they have failed. Every time ransomware is able to execute and encrypt data, our preventative controls have failed. We can use this incredibly destructive and annoying malware as a tool to learn about the shortcomings of our security program, or the digital canary in the digital coal mine (when the canary is dead it’s time to evacuate) so we can:
- Prevent and detect more ransomware and other malware incidents
- Be better able to defend our enterprises against more skilled and determined attackers such as organised crime and nation state funded actors
The point is that if ransomware can operate in your environment then there is little hope you have of being able to defend against the more skilled and determined attackers. The critical questions that must be answered is “how did the ransomware get through my perimeter controls?” and “how was it able to execute and encrypt data without being detected before a victim loses access to their critical business documents (and cat photos)?”
Detecting a threat in the environment is critical to minimising the damage malware does in the network, which is why we need multiple layers of controls to protect. We should not get too far into the preventative controls here, but like our mothers used to tell us “An ounce of prevention is worth a pound of cure” (my mother never went metric). There have been PLENTY of articles written about preventing ransomware and other malware so I do not want to rehash what has already been done. If you want to look for articles on prevention I suggest you have a read of the Cisco Talos blog “
Ransomware: Past, Present, and Future”.
One last word on prevention, before we move on to what we are here for. There’s a simple to deploy technique that is being overlooked by most information security professionals – blocking DNS lookups of known malicious sites. Cisco acquired OpenDNS in 2015. One of OpenDNS’ main functions is to provide a safe DNS infrastructure for name resolution services. The differentiator with OpenDNS over many standard DNS services is it provides protection by blocking name resolution for known malicious domains. The reason blocking DNS lookups for ransomware is effective, is that most, if not all, ransomware uses a multi-stage attack where an email is typically used to deliver the payload and when the payload executes it calls crypto.evil.com (for example) to generate an encryption key. Yes, it is not perfect as we are playing catch up, and would be preferable to prevent the initial infection, but if you don't get your data encrypted we can call that a win! More details of this functionality can be found
here.
Now lets get to the crux of concept of the canary in the coal mine analogy. What I’m trying to say is that the presence of ransomware is an indicator of bigger problems. You can think of ransomware as the (unfortunately) dead canary on the bottom of the cage that has detected the gas leak. I believe that you should be looking for the root cause of the ransomware incident rather than concentrating on your canary problem. Root cause analysis will show how the ransomware got into the enterprise and when you can understand that, you can start to fix the problem. Please do not go and buy a shiny new security object to fix the security problem before it is properly understood. Without fully understanding the problem you may be fixing something that will not improve your security posture commensurately. We all have the shiny object syndrome, but choose your time to act and resist the pressure from your peers as much as possible.
Consider the points I made above about:
- Malware (typically) comes into the network through the corporate email system
- Unknown software (ransomware) being able to run without human intervention on one of your corporate systems inside the corporate boundary
- Then connects to the outside world through your corporate proxy server, IPS and firewall(s)
This is remarkably like the tactics used by nation state attackers when setting up their beachhead inside the corporate boundary before stealing your intellectual property.
Starting to smell rotten eggs now? This is the real reason why we are so concerned about where ransomware can run, because if ransomware can run, so can nation state attackers and they can do a far sight more damage to your business than encrypting a few files. The typical motivation of nation state attackers is to steal your intellectual property, pricing information, customer data et. al. for the financial benefit of their own country.
This brings into a stronger focus the benefits of doing a proper root cause analysis of the ransomware incident as it’s not just about the one, two or more systems that run the latest ransomware variant and cause the ensuing mayhem of trying to minimise the damage and recover the data.
If you have planned ahead and have decent backups of your critical data (kudos to you if you have), then you don't need to get too spun up about the effects of the ransomware and the recovery is pretty straight forward. Make sure you learn the lesson that the ransomware incident has taught you. Find out how the ransomware got inside your organisation, and put in better controls to stop it happening again, or at least minimise the chance of it happening again (there’s no panacea for all ransomware). Then work out what it did on the endpoint and build a strategy for stopping from that happening again.
Next is to look at the network communications and determine how you could have a) disconnected it (e.g. blocking DNS calls to known malicious domains); or b) detected it earlier to minimise the damage.
One of the key differences between nation state attackers and the cybercriminals behind ransomware is the end goal. Cybercriminals are after money and typically the faster the better, whereas nation state attackers are playing the long game and looking for the data of choice. They want to maintain access and stay in your network for the long term, whilst extracting the data that they are looking for. Nation state attackers move laterally, hopping from system to system, looking for the data that they have been tasked with finding, and acquiring the administrator credentials often necessary to get access to this data. All of these actions have signatures, or indicators of compromise that you can detect with the right tools. If you have not looked for them, or had a skilled team working on your behalf, you might be shocked at what you discover.
The objective is to learn from the incident and make continuous improvements to your defences and detection capabilities. If ransomware can run in your environment, then so can the tools that nation state attackers use, and this is a cyber arms race against attackers, whether they be nation state, cybercriminals, or activists with a keyboard. So when you realise that the adversary is continuously improving their tools and techniques (as recently demonstrated by the cybercriminals and their ransomware campaigns), then you had better be doing the same to maintain your edge so your business can survive.
Remember that ransomware, whilst annoying and inconvenient, is just the canary in the coal mine. If your yellow bird is on the bottom of the cage, you’ve potentially got bigger problems.
Update: 20 July 2016
A new version of the Locky ransomware operates in offline mode so does not need to call back home to get encryption keys. Read the following
PC World piece for more details.
Guest Blog - First published by my colleague and good friend Goma and inspired by the Western Australia outback - not that there are many canaries there!