Yesterday’s Healthcare Security Leader
A mere ten years ago, if you worked with just about any hospital or healthcare provider you may have come across the Information Security Manager, Director of Security and Compliance, or someone who filled this role under another title. Their role was to lead ‘IT Security’ and manage a small staff of security administrators or analysts, whose role in turn, was to provision users to systems, and troubleshoot access problems. The team would also occasionally check firewall and other security logs when time permitted, amongst a myriad of other tasks and responsibilities, including vulnerability testing and HIPAA and PCI self-assessments.
Healthcare security teams usually were (and still are) smaller, less skilled and poorly paid compared to their peers in other industries. Their need to be generalists prevented them from specializing in key areas like threat analysis and incident response, or the development of deep technical security skills. Security was often an afterthought in IT architecture or development conversations, and usually seen somewhat negatively as being an obstacle to the release of new systems or feature improvements to older ones.
The security leader, even if they had a ‘CISO’ title, often reported into IT, usually below the CIO, CTO, or someone even more detached from the board. The conflict of interests between IT’s mission to provide technology systems for users, versus security’s mission to protect the enterprise was very apparent. Security usually lost most battles with IT as well as with end users over new requirements. Rebellions were commonplace against improved user security controls, even for something like the implementation of complex passwords rotated every 90 days - things we take for granted today. A mere ten years ago healthcare was a living bastion of the past; a loud and vociferous user base dominated by Physicians happy to take their complaints directly to the board or to threaten to take their business elsewhere. This ensured that nothing was put in the way of patient care – even a password! Such was the power that Physicians wielded.
Security was usually funded with whatever was left over or could be spared from the IT budget. Consequently it was seen as a drain on new tools and improved functionality for users. Whatever security received, it was usually way too small to do much with.
Occasional vulnerability and penetration testing along with compliance assessments against HIPAA, PCI and security frameworks like ISO and NIST were duly reported to CIO, CTO, or the designated compliance officer, complete with a list of identified gaps. However remediation of gaps was usually given little priority compared to the IT mission to build and release new application functionality “required” by the business. That is, a business, run and largely controlled by clinicians and a business focused more or less solely on providing patient care.
It was doubtful that the hospital or healthcare board of directors was ever provided with specific details of any such security audits or assessments, merely informed that the covered entity was compliant with HIPAA, PCI and any other regulatory requirements (if the subject came up at all). The security leader had no direct access to the board, and was considered too junior to address these chieftains in person. Even if offered the opportunity, the
security leader would probably talk in a language that the board wouldn’t understand. Security leaders were largely kept in the shadows, their message relayed and filtered by the CIO or CTO.
 Today’s Healthcare Security Leader
Today’s Healthcare Security Leader
Move ahead ten years and the picture has begun to change. Larger healthcare providers have an executive level security leader, or even a Chief Information Security Officer (CISO) who, while they may still report to the Chief Information Officer or Chief Compliance Officer, will have a seat at the table for quarterly board meetings and may now chair sub-committees on security, privacy and compliance.
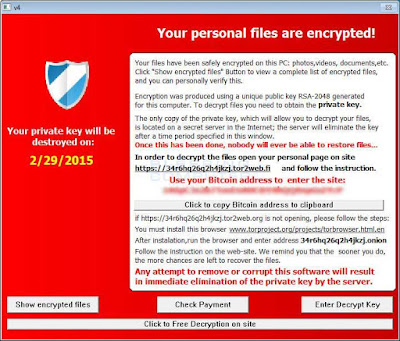
Security is now recognized as one of the most important enterprise risks by healthcare boards of directors. Media fixation with security breaches at other provider or payer organizations, complete with news of fines, penalties and reciprocity to patients whose information may have been disclosed has ensured this. So too has media attention to ransomware outbreaks at health providers and the encryption of hospital data and IT systems needed to treat patients. Such is the power of the media and the impact to business revenues and reputation when security incidents occur.
This increased focus on security by the board is leading to demands for not only regular situation reporting on security, privacy and risks from the CISO, but also reporting from the CTO, COO, CFO and CEO on what is being done to address identified risks. In the course of ten years, Security Leadership reporting has gone from almost unnoticed to 'center stage'.
In fact, corporate boards are now in some cases directly appointing
external highly experienced CISOs to lead security and to act as change agents across the organization. These 'Change Agent’ or 'Advisory' CISOs are often brought in from leading security organizations or from the Big 4 audit firms. They are deployed for a finite period of time in order to achieve rapid advancement in the security, risk, and compliance posture of the organization and to get up and going, a security program that can be taken over my a more junior full time replacement once the Interim leader has done his or her work.
Despite this recent focus, according the
Cisco Security Capabilities Benchmark Study (PDF) healthcare organizations are still not implementing as full an array of strong security defenses as organizations in other industries. Furthermore, the report claims that healthcare organizations are more likely than those in other industries, to try to manage their security needs internally instead of outsourcing services such as monitoring, incident response, remediation, and auditing. This slowness to embrace expert services in key specialty areas, may account for the recent spike in healthcare breaches as hackers focus their attention on easy targets.
The same survey also indicated that CISOs tend to be more optimistic than their SecOps colleagues about their security protections. It could be that as security leadership gets further away from the hands-on defense of the realm, so too does their realization of the ability of healthcare, to respond to a threat landscape that changes almost daily.
Healthcare is after all, under attack as widely reported in previous articles and publications!
Given the scarcity of security resources, and the ability of healthcare to attract and retain such professionals in a highly competitive market, this is hardly surprising. According to
Cisco’s 2015 Mid Year Security Report there is now a 12x demand over supply for qualified or experienced security professionals, and despite limited success to hire or grow additional security resources, healthcare simply cannot onboard enough security staff to defend itself against current attacks.
The result is that many healthcare providers are now looking at ways to maximize the effectiveness of their limited security staffs, by consuming managed security services for much of their
security operations threat detection (PDF) and
incident response (PDF) in order to free up security team members for higher value tasks.
This change in focus was recently identified in the
Cisco 2016 Annual Security Report.
As security professionals become aware of threats, they may be seeking ways to improve their defenses for example, by outsourcing security tasks that can be managed more efficiently by consultants or vendors. In 2015, 47 percent of our surveyed companies outsourced security audits, an increase from 41 percent in 2014. Also in 2015, 42 percent outsourced incident response processes, compared with 35 percent in 2014. (See figure below)
In addition, more security leaders are outsourcing at least some security functions. In 2014, 21 percent of the survey respondents said they did not outsource any security services. In 2015, that number dropped significantly, to 12 percent. Fifty-three percent said they outsource services because doing so was more cost-efficient, while 49 percent said they outsource services to obtain unbiased insights.

While healthcare security leadership and better visibility has greatly improved the size breadth and expertise of security teams, it has by and large, made only limited advances to overall security, fueled in part by limitations on security budgets and the availability of additional or specialist security professionals. At the same time, the enormity of the threats leveled against healthcare payer, provider and pharmaceutical organizations has grown exponentially, creating further gaps in security. The need for security leaders to evaluate security needs holistically and to spend money wisely is perhaps more important now than ever before.
Information Security is also not immune to the ‘Do More With Less’ mantra that is affecting all areas of business, and must be creative in how it allocates its resources, and selective where it spends its money. Looking for opportunities to improve efficiencies while at the same time improving the probability of security outcomes, is now the new ‘modus operandi’ for security leaders.
 Tomorrow’s Healthcare Security Leader
Tomorrow’s Healthcare Security Leader
The security leader of tomorrow will be an executive in charge of his or her own budget, staff and the procurement where it makes sense, of vendor provided security functions that can be consumed as a service, often better, cheaper and faster than developing or running these from within. In the same way that the cloud has changed application development and the internal data center, so too will the consumption of security services.
Tomorrow’s security leader will also more than likely be titled ‘CISO’, or 'CSO', fulfilling the role of information security leadership and governance. They will likely report outside of IT to the COO, CFO or directly to the CEO. They might even sit at the right hand of the CEO in board meetings, and will be instrumental in helping to maintain the confidence of the CEO in the eyes of the board.
During the dot-com bubble we used to talk of an ‘Internet Year’ being nothing more than a few months or weeks. Its not surprising then, that in the period of a mere ten solar years, the role of the healthcare security leader has evolved an ‘Internet millennium’.
Given the almost exponential change in cybersecurity, how many solar years will it take for the healthcare security leadership role to evolve another Internet millennium?
What cybersecurity event or series of events will accelerate this shift in paradigm – of not just security leadership and governance, but also healthcare security posture and spend?
Will it require a hospital system to be sued out of business following a massive breach of patient, financial or other critical healthcare information? Or will healthcare leadership pro-actively address its business-life-threatening risks before its too late?
This blog was originally published to http://blogs.cisco.com/security/the-changing-face-of-the-healthcare-security-leader